- January 23rd, 2026
How to Verify Identities Against AI-Powered Impersonation Use out-of-band verification through channels[...]
- January 23rd, 2026
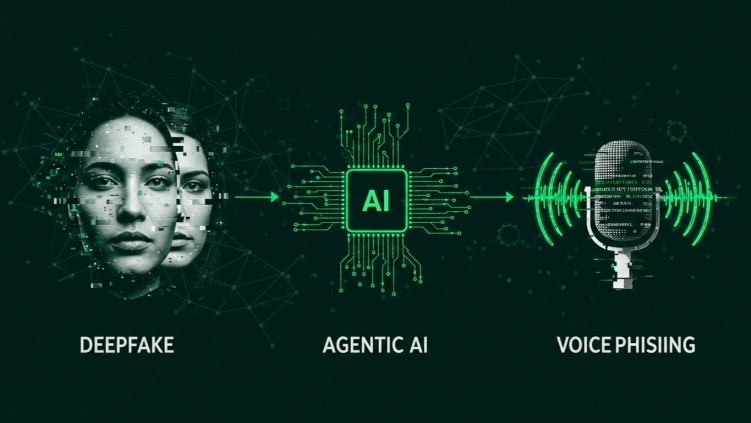
Will deepfake watermarks and regulation protect organizations from criminal attacks? No. Deepfake[...]
Most security awareness training platforms were designed for email phishing. They are[...]
- January 23rd, 2026
AI-driven social engineering disproportionately targets a small number of high-risk roles inside[...]
- January 23rd, 2026
Training employees to visually identify deepfake glitches is ineffective because modern AI-generated[...]
- January 23rd, 2026
Do most awareness training platforms protect against deepfakes? No. Most awareness training[...]
- January 23rd, 2026
How to Choose a Deepfake Simulation Platform for Your MSP Practice Your[...]
Red Teaming
Pen Testing
Deepfake Simulations
Teams Phishing
Video Conferencing Phishing
Deepfake Avatars
For CISOs & Security Directors
Deepfake Simulations
Managed Training
Micro Modules
AI Educational Bots
Video Production
Deepfake Avatars
For Security Awareness Managers