- December 29th, 20250 comments on Threat Intelligence-Based Awareness Training
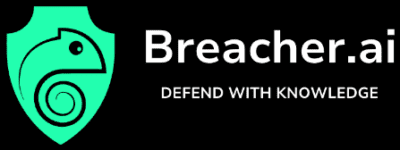
Threat Intelligence-Based Awareness Training Your employees train against templates. Attackers[...]
- December 23rd, 2025
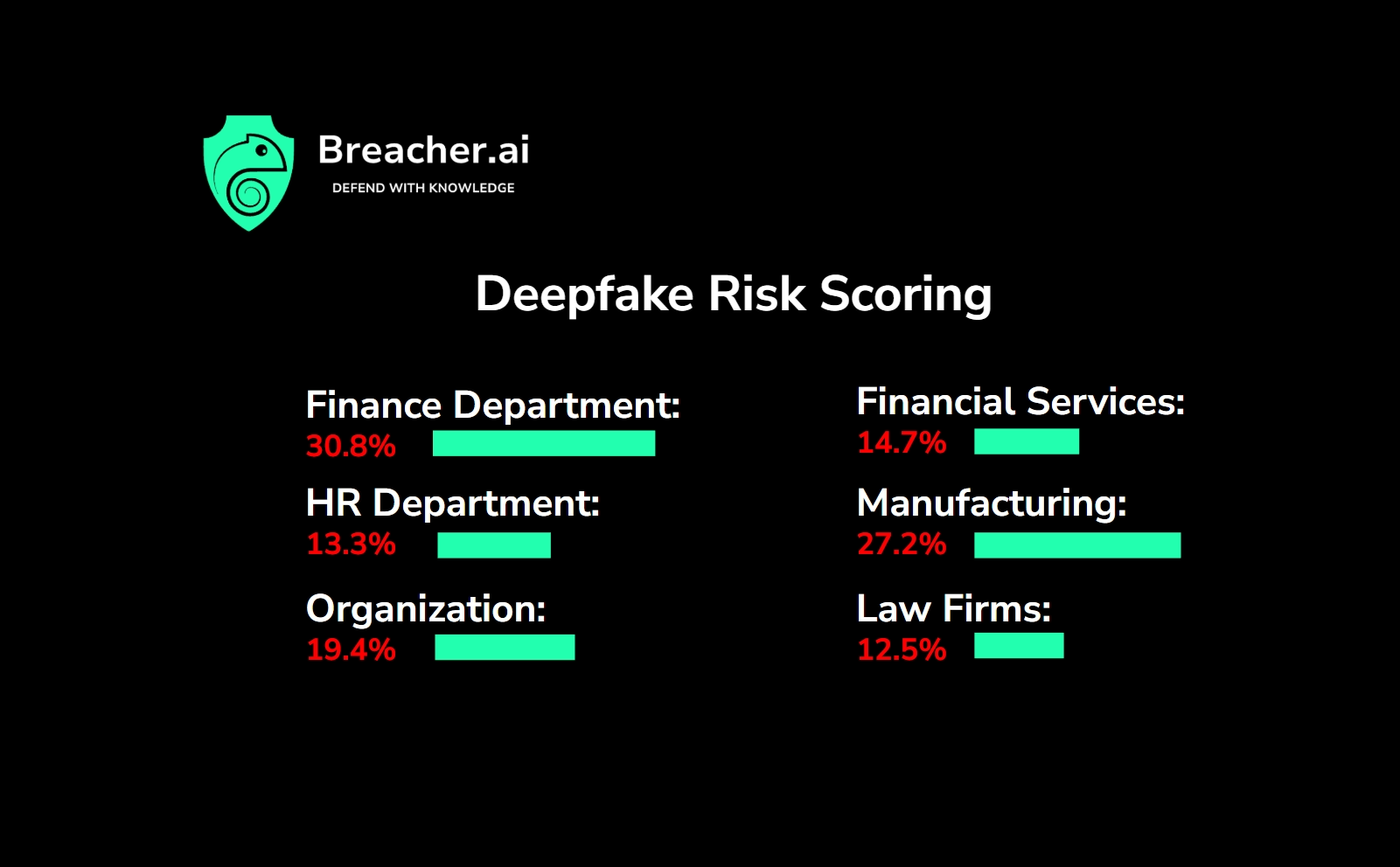
Deepfake Risk Assessment: Know Where You Stand Before Attackers Do A[...]
- December 11th, 2025
How CISOs Can Tackle Deepfakes and AI-Powered Attacks in 2026: A[...]
- November 1st, 2025
Why Your Human Risk Management Strategy Needs Three Layers. Is Your AUP[...]
- October 19th, 2025
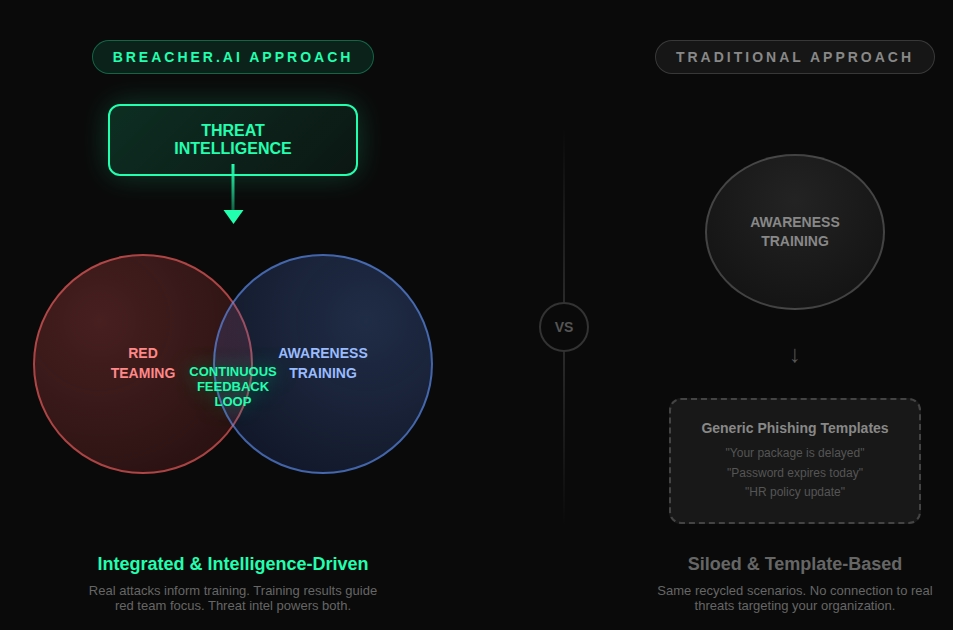
Our patent pending approach gives you a benchmark risk score against similar[...]
- October 5th, 2025
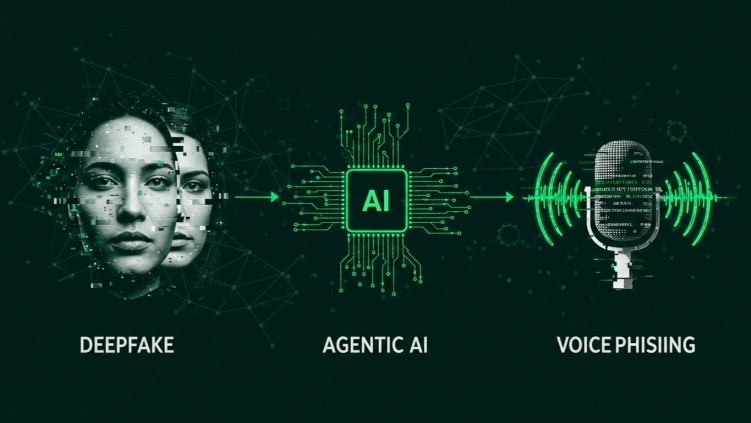
The Convergence Vector: Where Agentic AI, Deepfakes, and Voice Phishing Intersect[...]
Red Teaming
Pen Testing
Deepfake Simulations
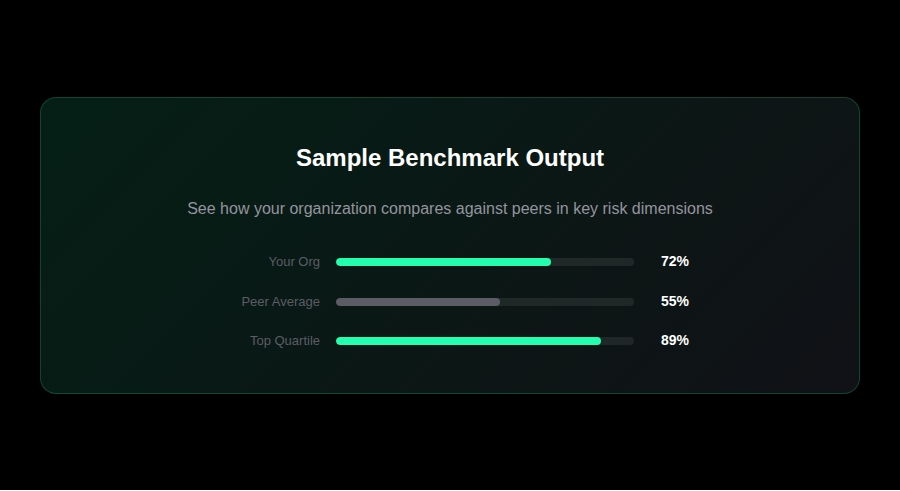
Teams Phishing
Video Conferencing Phishing
Deepfake Avatars
For CISOs & Security Directors
Deepfake Simulations
Managed Training
Micro Modules
AI Educational Bots
Video Production
Deepfake Avatars
For Security Awareness Managers